The web is great. You can talk to people on the other side of the planet and not even notice a delay. But that one connection goes through numerous unknown machines from you to them and back again. Some formats like email can even leave copies of themselves laying all over the world. That super embarassing secret you’re telling your best friend, your credit card or banking details, some things you just don’t want other people to know. That’s where Secure Socket Layers (SSL) Certificates come in.
Stay with me, I’m going to avoid most of the tech talk, but I hope to explain how they work for websites. Basically it’s the difference between http:// and https:// at the start of a website address. http:// means everything is straight-forward, and in the clear. Including, usually, passwords. https:// on the other hand means you are connected through SSL, and the communication is encrypted. Meaning people trying to overhear your digital conversation can’t make out what’s going on. (But note, as someone on twitter said, https:// means “private”, not “to be trusted”, afterall you might be having a private conversation with Satan.)
Whenever you’re doing something important on the internet it is a good idea to check for https:// and other indicators like little padlock symbols your browser displays. And to take heed of certificate warnings from websites you have visited before.
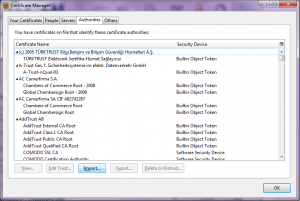
But, how does this encrypted conversation happen? Even with a website you’ve never been to before? Well, there are things called Certification Authorities (CAs). These are trusted-third parties (usually companies) who vouch for the correctness of the SSL cert. They can do this because they have a proven track record, and the people who make your browser (Microsoft, Apple, Mozilla, etc) saw fit to include their root certs in your browser by default. Want to see all the CAs trusted by your browser? I’m using FireFox, but you can easily find the coressponding values in your browser, or through a quick internet search. Open up Tools->Options, go to the Advanced tab, and then the Encryption sub-tab.
If you click the “View Certificates” button you open up the Certificate Manager in another window.
You can see the long list of CAs under the Authorities tab. (There are other tabs with other kinds of certs as well, but we’ll leave them for a future post.) Bet you didn’t realise you were so trusting.
So what does all this have to do with TOG? You’re probably viewing this site through http://www.tog.ie, but we also have a https:// version of the site available as well. … If you just tried it you’ve probably gotten a warning from your browser, telling you that we can’t be trusted. Well, that’s up to you to decide, but let me explain about the cert.
Most of the CAs prepopulated in your browser are commerical entities. They charge money for their services. They also often require a lot of personal information to get a cert (so that they can determine trustworthiness). TOG has server admins that care about privacy and non-commerical alternatives. Our cert comes from CAcert.org, an organisation with similar values. But, CAcert is not included in any browsers CA lists, yet. So when you visit https://www.tog.ie you get the warning: “The certificate is not trusted because the issuer certificate is not trusted.”.
To avoid getting these warnings everytime you can permanently add the cert for tog.ie to your browser (via the warning screen itself). Or, to trust any site with a cert from CAcert, go to CAcert and import their root certificate. On that page you’ll find three types of certs. What you want is the Class 1 PKI Key root cert, probably in PEM format.
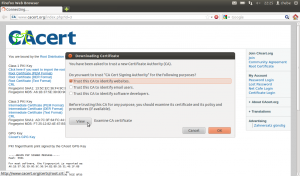
When you click on the cert you may be prompted as to what purposes you wish to accept this cert. For our purposes “Trust this CA to identify websites” is fine. Then that’s it. You trust one more CA, and can visit SSL secured sites that use its certs without warnings getting in your way.
Phew, that was a mouthful, time for a cup of tea.